Whereas blue groups defend, pink groups assault. They share a standard objective, nevertheless – assist determine and handle gaps in organizations’ defenses earlier than these weaknesses might be exploited by malicious actors. The blue/pink staff workout routines present invaluable insights throughout the technical, procedural and human sides of safety and might finally assist organizations fend off precise assaults.
We not too long ago checked out a couple of open-source instruments that blue groups could use whereas defending towards simulated assaults, in addition to at 4 devices that might, within the improper fingers, trigger safety bother. This time round, we’ll spherical up 5 cutting-edge, compact instruments that hobbyist {hardware} hackers in addition to pink teamers or moral hackers could wield whereas honing their abilities or doing their job.
1. Raspberry Pi 5
Thanks particularly to its versatility, energy and vibrant community-driven ecosystem, the Raspberry Pi has turn into a popular instrument amongst safety professionals, college students, and lovers alike. Primarily an inexpensive single-board laptop, Raspberry Pi can be loaded with numerous penetration testing instruments and serve a number of roles.
It could actually, for instance, ‘morph’ right into a community sniffer and seize packets for detailed evaluation or run scripts for automated safety assessments. It’s additionally excellent for on-the-go testing of instruments and for analyzing Web of Issues (IoT) gadgets, figuring out vulnerabilities earlier than cybercriminals have the possibility to use them.
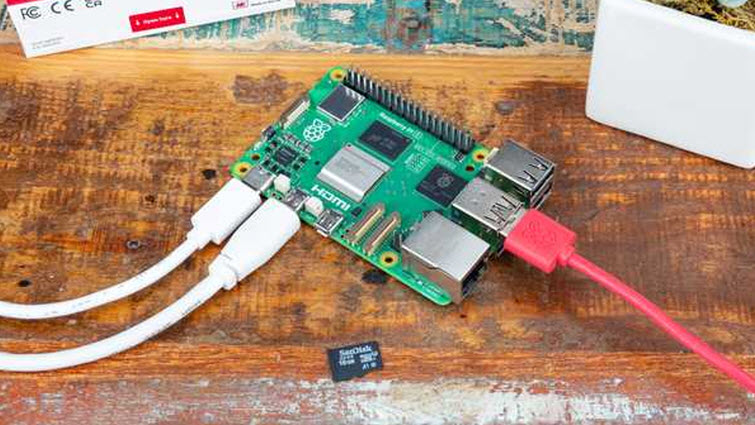
The Raspberry Pi helps quite a lot of working techniques tailor-made to completely different functions and person preferences. Its official working system, Raspberry Pi OS (previously Raspbian), relies on Debian Linux and is optimized for the ARM structure.
Moreover, standard distributions like Kali Linux can be found, and so they’re particularly crafted for penetration testing and safety auditing. These distributions come pre-loaded with a collection of instruments for community scanning, vulnerability evaluation, wi-fi assaults, and extra.
Additionally, listed below are a couple of attention-grabbing instruments and tasks that may leverage Raspberry Pi because the underlying {hardware} platform:
- FruityWifi: Used to audit wi-fi networks and allow superior assaults through an internet interface.
- Ha-Pi: Supplies instruments for penetration testing, together with Aircrack Ng Suite and Metasploit.
- Raspberry Pwn: Consists of instruments like scapy, Wireshark, and tcpdump.
- Wi-fi Assault Toolkit (WAT): Performs Wi-Fi community penetration testing on ARM platforms.
- PwnPi: A simplified model of Debian Wheezy for pentesting.
- NetPi: A undertaking aimed toward making a community analyzer with commercial-grade options.
2. HackRF One
The HackRF One is a Swiss military knife for radio frequency (RF) lovers and professionals alike. This open-source system lets everyone from curious hobbyists to seasoned professionals dive into the invisible ocean of RFs and discover and manipulate the waves that carry every little thing out of your favourite music station to crucial communication indicators.
Designed to be versatile, this single-board software-defined radio (SDR) peripheral can each transmit and obtain indicators from 1 MHz to six GHz. This huge vary means you’ll be able to experiment with nearly any kind of wi-fi communication, from AM/FM radio to Wi-Fi and even satellite tv for pc indicators. It’s nearly like having the keys to each wi-fi protocol ever conceived, multi function compact type issue.
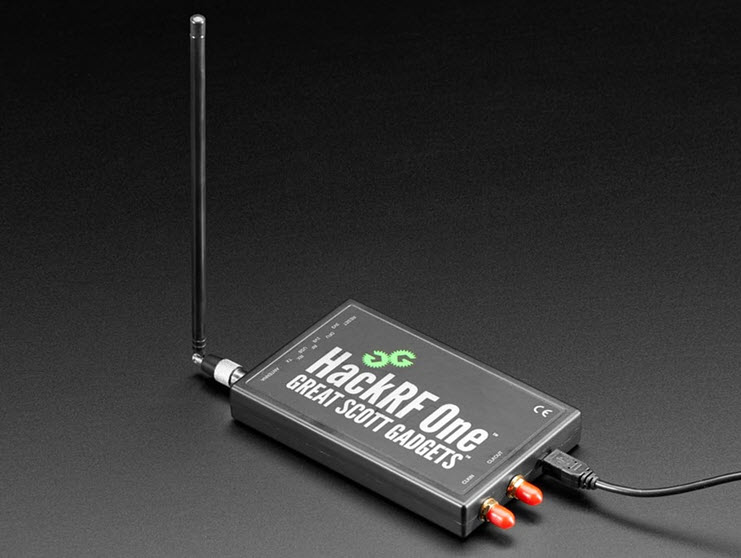
Regardless of its superior capabilities, HackRF One is transportable and strong sufficient for fieldwork, permitting safety professionals to check wi-fi community vulnerabilities or RF engineers to troubleshoot sign points on the go.
Talking of which, it enables you to assess the safety of wi-fi techniques, carry out replay assaults, and discover the vulnerabilities of IoT gadgets. This consists of emulating and analyzing automotive distant controls, alarms, and different gadgets, manipulating GPS indicators, speaking with RFID tags, and performing sign evaluation and satellite tv for pc communication monitoring.
3. WiFi Pineapple
Admittedly, it’s possible you’ll want a bigger pocket for this one, however this glossy gadget that appears like an innocuous router holds the ability to uncover the hidden secrets and techniques of wi-fi networks. The WiFi Pineapple is used for probing the safety of wi-fi networks by simulating a traditional entry level the place it attracts unsuspecting customers. It has two community interfaces: one for offering web entry and the opposite for interacting with close by Wi-Fi gadgets.

On the core of the WiFi Pineapple is its customized working system, Pineapple OS. This Linux-based OS is particularly meant for wi-fi penetration testing and comes pre-loaded with a plethora of highly effective instruments. Pineapple OS gives a steady and environment friendly setting, guaranteeing that the system operates easily throughout complicated safety assessments.
Key functions:
- Evil twin assaults: Creates rogue entry factors to intercept community visitors and collect delicate info.
- Deauth assessments: Forces disconnections from reliable networks to allow man-in-the-middle assaults.
- Safety assessments: Identifies vulnerabilities and configuration gaps in wi-fi networks.
- Managed assaults: Helps directors perceive and develop higher safety insurance policies.
- Versatile performance: Supplies numerous automated and guide wi-fi community pentesting instruments.
4. Deauther Watch
The identify says all of it. Basically a wearable that integrates capabilities for executing Wi-Fi deauthentication assaults, this gadget disrupts the Wi-Fi connection between a tool (akin to a smartphone, laptop computer, or IoT system) and a Wi-Fi router by sending specifically crafted deauthentication packets.
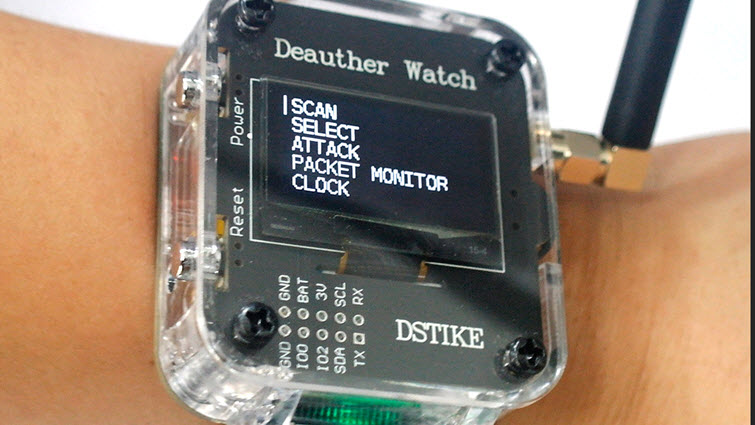
Moreover, the Deauther Watch could include options akin to Wi-Fi scanning and monitoring, and packet capturing to detect vulnerabilities or monitor community exercise. The ESP8266 Deauther V3 software program gives a command-line interface (CLI) through USB and assessments 2.4 GHz WiFi networks for vulnerabilities.
5. Ubertooth One
The Ubertooth One is primarily designed for monitoring Bluetooth communications and analyses of Bluetooth packets, in addition to for the testing of Bluetooth-enabled Web of Issues (IoT) gadgets. This open-source gadget helps numerous safety testing situations, together with sniffing for delicate info exchanged over Bluetooth connections. Certainly, its capabilities of lengthen past typical Bluetooth adapters and it may be personalized to satisfy particular safety testing wants.
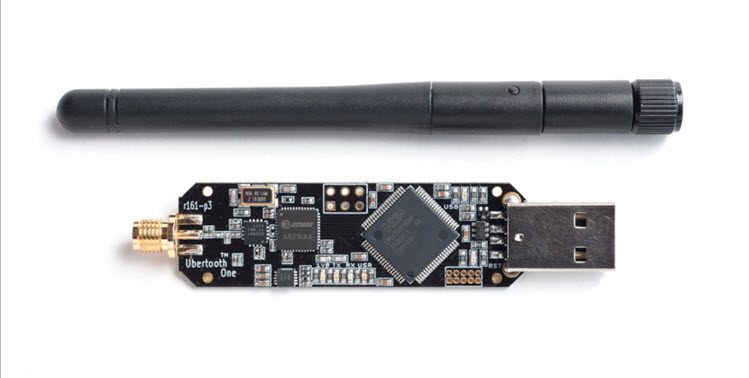
It’s based mostly on the GreatFET platform and encompasses a succesful radio transceiver chipset. The Ubertooth One operates within the 2.4 GHz ISM band and helps Bluetooth Low Vitality (BLE) and Traditional Bluetooth protocols, making it versatile sufficient to sort out a variety of functions.
Conclusion
As with all devices of this sort, moral concerns are paramount. The tech must be utilized in environments and conditions the place permission is granted, akin to in managed testing environments or for academic functions. Certainly, utilizing them to conduct unsanctioned assaults is illegitimate in lots of jurisdictions and might include extreme penalties. In the meantime, organizations must implement a mixture of technical measures, insurance policies, and person training in order that they keep protected from unauthorized use of those gadgets on their networks.

