A ransomware group known as Darkish Angels made headlines this previous week when it was revealed the crime group just lately acquired a document $75 million information ransom cost from a Fortune 50 firm. Safety specialists say the Darkish Angels have been round since 2021, however the group doesn’t get a lot press as a result of they work alone and keep a low profile, choosing one goal at a time and favoring mass information theft over disrupting the sufferer’s operations.
Picture: Shutterstock.
Safety agency Zscaler ThreatLabz this month ranked Darkish Angels as the highest ransomware risk for 2024, noting that in early 2024 a sufferer paid the ransomware group $75 million — larger than any beforehand recorded ransom cost. ThreatLabz discovered Darkish Angels has carried out among the largest ransomware assaults to this point, and but little is understood in regards to the group.
Brett Stone-Gross, senior director of risk intelligence at ThreatLabz, mentioned Darkish Angels function utilizing a wholly completely different playbook than most different ransomware teams. For starters, he mentioned, Darkish Angels doesn’t make use of the standard ransomware affiliate mannequin, which depends on hackers-for-hire to put in malicious software program that locks up contaminated methods.
“They actually don’t wish to be within the headlines or trigger enterprise disruptions,” Stone-Gross mentioned. “They’re about earning profits and attracting as little consideration as attainable.”
Most ransomware teams keep flashy sufferer leak websites which threaten to publish the goal’s stolen information until a ransom demand is paid. However the Darkish Angels didn’t actually have a sufferer shaming web site till April 2023. And the leak web site isn’t notably properly branded; it’s known as Dunghill Leak.
The Darkish Angels sufferer shaming web site, Dunghill Leak.
“Nothing about them is flashy,” Stone-Gross mentioned. “For the longest time, they didn’t even wish to trigger an enormous headline, however they in all probability felt compelled to create that leaks web site as a result of they needed to point out they had been critical and that they had been going to publish sufferer information and make it accessible.”
Darkish Angels is regarded as a Russia-based cybercrime syndicate whose distinguishing attribute is stealing actually staggering quantities of information from main firms throughout a number of sectors, together with healthcare, finance, authorities and schooling. For giant companies, the group has exfiltrated between 10-100 terabytes of information, which might take days or perhaps weeks to switch, ThreatLabz discovered.
Like most ransom gangs, Darkish Angels will publish information stolen from victims who don’t pay. A number of the extra notable victims listed on Dunghill Leak embrace the worldwide meals distribution agency Sysco, which disclosed a ransomware assault in Might 2023; and the journey reserving big Sabre, which was hit by the Darkish Angels in September 2023.
Stone-Gross mentioned Darkish Angels is commonly reluctant to deploy ransomware malware as a result of such assaults work by locking up the goal’s IT infrastructure, which usually causes the sufferer’s enterprise to grind to a halt for days, weeks and even months on finish. And people sorts of breaches are likely to make headlines shortly.
“They selectively select whether or not they wish to deploy ransomware or not,” he mentioned. “In the event that they deem they’ll encrypt some information that received’t trigger main disruptions — however will give them a ton of information — that’s what they’ll do. However actually, what separates them from the remainder is the quantity of information they’re stealing. It’s an entire order of magnitude larger with Darkish Angels. Corporations shedding huge quantities of information can pay these excessive ransoms.”
So who paid the document $75 million ransom? Bleeping Pc posited on July 30 that the sufferer was the pharmaceutical big Cencora (previously AmeriSourceBergen Company), which reported a knowledge safety incident to the U.S. Securities and Trade Fee (SEC) on February 21, 2024.
The SEC requires publicly-traded firms to reveal a doubtlessly materials cybersecurity occasion inside 4 days of the incident. Cencora is at present #10 on the Fortune 500 checklist, producing greater than $262 billion in income final yr.
Cencora didn’t reply to questions on whether or not it had made a ransom cost in reference to the February cybersecurity incident, and referred KrebsOnSecurity to bills listed underneath “Different” within the restructuring part of their newest quarterly monetary report (PDF). That report states that almost all of the $30 million price in “Different” was related to the breach.
Cencora’s quarterly assertion mentioned the incident affected a standalone legacy data know-how platform in a single nation and the international enterprise unit’s capacity to function in that nation for roughly two weeks.
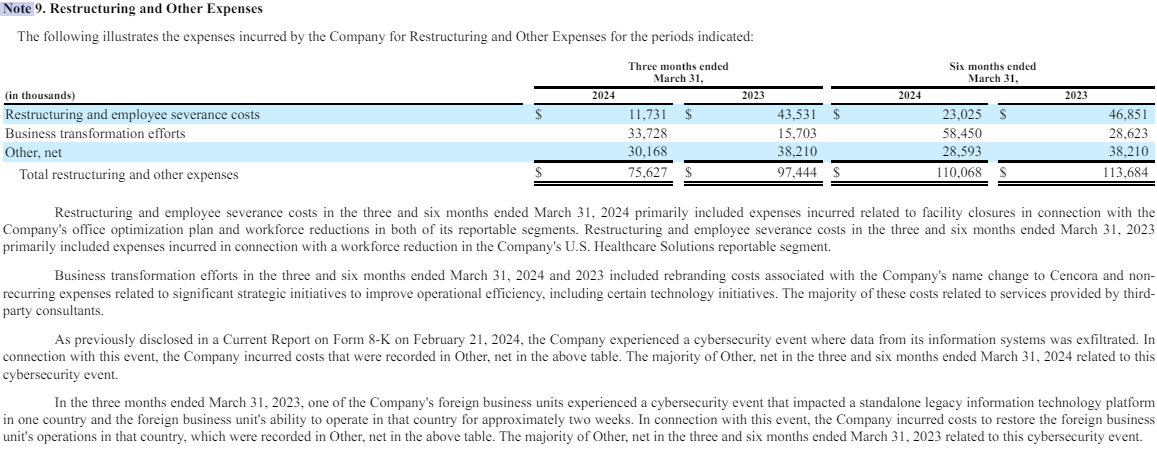
Cencora’s 2024 1st quarter report paperwork a $30 million price related to a knowledge exfiltration occasion in mid-February 2024.
In its most up-to-date State of Ransomware report (PDF), safety agency Sophos discovered the typical ransomware cost had elevated fivefold previously yr, from $400,000 in 2023 to $2 million. Sophos says that in additional than four-fifths (82%) of instances funding for the ransom got here from a number of sources. Total, 40% of complete ransom funding got here from the organizations themselves and 23% from insurance coverage suppliers.
Additional studying: ThreatLabz ransomware report (PDF).

