Microsoft on Tuesday launched 117 patches touching 15 product households. Three of the addressed points, affecting Configuration Supervisor, Visible Studio, and Home windows, are thought of by Microsoft to be of Essential severity. At launch time, two of the problems addressed are recognized to be below exploit within the wild, with eight further CVEs extra prone to be exploited within the subsequent 30 days by the corporate’s estimation. Three of this month’s points are amenable to detection by Sophos protections, and we embrace info on these in a desk beneath.
Along with these patches, the discharge contains advisory info on 4 Edge-related CVEs and one associated to curve (affecting CBL Mariner and Home windows), together with the same old servicing stack updates. We’re as all the time together with on the finish of this submit further appendices itemizing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product household.
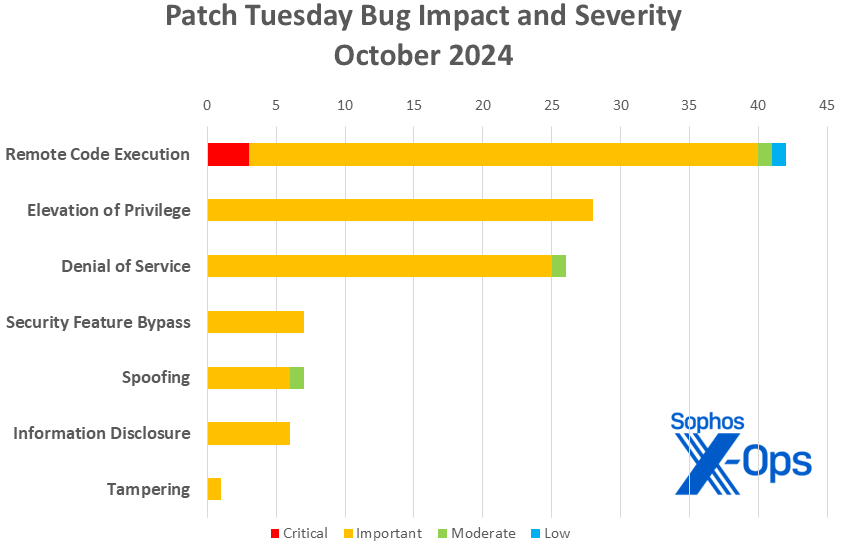
By the numbers
- Complete CVEs: 117
- Publicly disclosed: 4
- Exploited detected: 2
- Severity
- Essential: 3
- Essential: 110
- Reasonable: 3
- Low: 1
- Impression
- Distant Code Execution: 42
- Elevation of Privilege: 28
- Denial of Service: 26
- Safety Characteristic Bypass: 7
- Spoofing: 7
- Data Disclosure: 6
- Tampering: 1
- CVSS base rating 9.0 or higher: 2
- CVSS base rating 8.0 or higher: 25
Determine 1: Denial of service points make a exceptional exhibiting on this month’s patch assortment thanks partly to numerous Home windows Cell broadband-driver patches; extra on that in a second
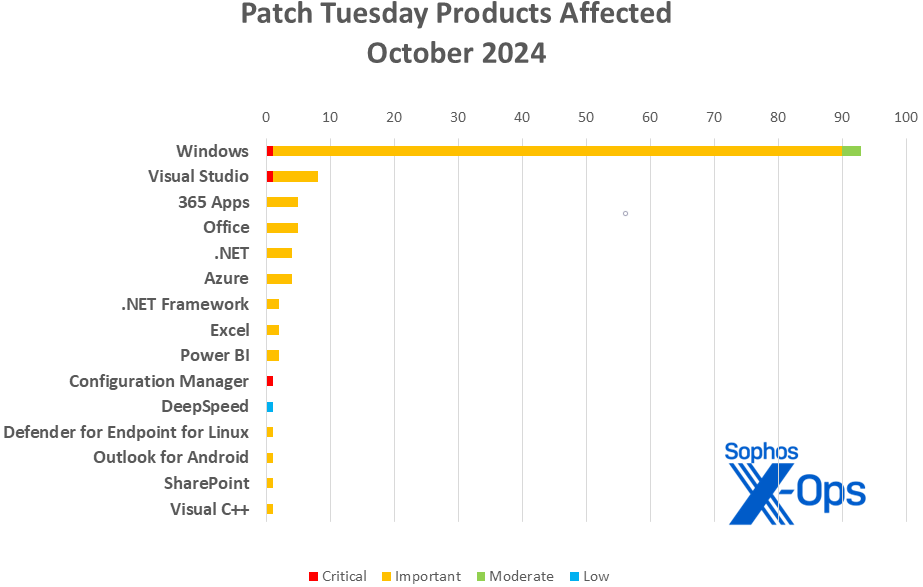
Merchandise
- Home windows: 93
- Visible Studio: 8
- 365 Apps: 5
- Workplace: 5
- .NET: 4
- Azure: 4
- .NET Framework: 2
- Excel: 2
- Energy BI: 2
- Configuration Supervisor: 1
- DeepSpeed: 1
- Defender for Endpoint for Linux: 1
- Outlook for Android: 1
- SharePoint: 1
- Visible C++: 1
As is our customized for this record, CVEs that apply to a couple of product household are counted as soon as for every household they have an effect on.
Determine 2: A couple of hardly ever seen product households make an look on this month’s chart, however Home windows guidelines the roost
Notable October updates
Along with the problems mentioned above, numerous particular gadgets benefit consideration.
CVE-2024-38124 – Home windows Netlogon Elevation of Privilege Vulnerability
CVE-2024-43468 — Microsoft Configuration Supervisor Distant Code Execution Vulnerability
Each of this month’s CVEs with CVSS base scores of 9.0 or above include mitigation recommendation. The Config Supervisor situation (CVE-2024-43468), the extra extreme of the 2 with a 9.8 CVSS, additionally has particular directions. For the Netlogon situation (CVE-2024-38124), the next mitigations are supplied (textual content courtesy of Microsoft):
- Predictable Naming Conventions: Keep away from utilizing predictable naming conventions for area controllers to forestall attackers from renaming their machines to match the following title to be assigned to a brand new area controller.
- Safe Channel Validation: Make sure that the safe channel is validated in opposition to extra than simply the pc title of the machine it was delivered to. This can assist forestall attackers from impersonating the area controller by acquiring the deal with and ready for the appointment to occur.
- Monitor for Renaming Actions: Implement monitoring for any suspicious renaming actions of computer systems throughout the community. This can assist with early detection and prevention of potential assaults.
- Enhanced Authentication Mechanisms: Think about using enhanced authentication mechanisms that transcend the present validation strategies to make sure the authenticity of the area controller and the safe channel.
As for the Configuration Supervisor situation, there are further steps required (textual content, once more, courtesy of Microsoft):
Clients utilizing a model of Configuration Supervisor specified within the Safety Updates desk of this CVE want to put in an in-console replace to be protected. Steering for how you can set up Configuration Supervisor in-console updates is accessible right here: Set up in-console updates for Configuration Supervisor.
The mitigation steerage for the Configuration Supervisor situation additionally recommends that directors specify an alternate service account, quite than the Pc account; extra info is accessible right here.
[15 CVEs] – Home windows Cell Broadband Driver DoS and RCE points
None of those points are as regarding because the Essential-severity CVE-2024-38161 cellular broadband driver situation patched again in July, however the sheer quantity is exceptional, as is the truth that all of those require bodily entry (to plug in a USB drive) or proximity (ample for radio transmission).
CVE-2024-43485 — .NET and Visible Studio Denial of Service Vulnerability
This Essential-severity Denial of Service situation casts its .internet quite extensively, affecting the platform not solely on Home windows however on Linux and macOS.
CVE-2024-43497 — DeepSpeed Distant Code Execution Vulnerability
It’s not frequent for a Low-severity situation to be named within the Patch Tuesday launch, however this one’s attention-grabbing for one more purpose – it impacts DeepSpeed, Microsoft’s speed-and-scale optimization booster for deep-learning coaching. (We consider this to be the first-ever Patch Tuesday bug affecting DeepSpeed, in addition to the primary Microsoft discover credited to an AI-specific bug-bounty program.)
CVE-2024-43527 — Home windows Kernel Elevation of Privilege Vulnerability
CVE-2024-43571 — Sudo for Home windows Spoofing Vulnerability
These two patches are much less notable for what they’re (although some observers could also be startled to see speak of sudo in a Patch Tuesday submit) than for what model of Home windows they have an effect on. Each of those Essential-severity patches have an effect on solely Home windows 11 24H2, the OS model getting into basic launch this week.
CVE-2024-43573 — Home windows MSHTML Platform Spoofing Vulnerability
One of many two vulnerabilities recognized to be below lively exploit within the wild, this Reasonable-severity Spoofing situation will get into the Halloween spirit by invoking the ghost of Web Explorer. Clients who obtain Safety Solely updates are inspired to use the IE Cumulative updates to exorcise this vulnerability.
Determine 3: As we enter the final quarter of the 12 months, Denial of Service points are catapulted into third place on the leaderboard, whereas the DeepSpeed bug places a Low-severity patch on the board for the primary time in 2024
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2024-43502 | Exp/2443502-A | Exp/2443502-A |
| CVE-2024-43572 | SID: 2310213; Troj/XML-AA, Troj/PastaLdr-A | SID: 2310213 |
| CVE-2024-43573 | SID: 2310220, 2310222; Exp/2443573-A | SID: 2310220, 2310221 |
As you may each month, if you happen to don’t need to wait on your system to tug down Microsoft’s updates itself, you may obtain them manually from the Home windows Replace Catalog web site. Run the winver.exe software to find out which construct of Home windows 10 or 11 you’re operating, then obtain the Cumulative Replace bundle on your particular system’s structure and construct quantity.
Appendix A: Vulnerability Impression and Severity
This can be a record of October patches sorted by affect, then sub-sorted by severity. Every record is additional organized by CVE.
Distant Code Execution (42 CVEs)
| Essential severity | |
| CVE-2024-43468 | Microsoft Configuration Supervisor Distant Code Execution Vulnerability |
| CVE-2024-43488 | Visible Studio Code extension for Arduino Distant Code Execution Vulnerability |
| CVE-2024-43582 | Distant Desktop Protocol Server Distant Code Execution Vulnerability |
| Essential severity | |
| CVE-2024-30092 | Home windows Hyper-V Distant Code Execution Vulnerability |
| CVE-2024-38029 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-38212 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38229 | .NET and Visible Studio Distant Code Execution Vulnerability |
| CVE-2024-38261 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38262 | Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability |
| CVE-2024-38265 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43453 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43480 | Azure Service Cloth for Linux Distant Code Execution Vulnerability |
| CVE-2024-43504 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-43505 | Microsoft Workplace Visio Distant Code Execution Vulnerability |
| CVE-2024-43517 | Microsoft ActiveX Information Objects Distant Code Execution Vulnerability |
| CVE-2024-43518 | Home windows Telephony Server Distant Code Execution Vulnerability |
| CVE-2024-43519 | Microsoft WDAC OLE DB supplier for SQL Server Distant Code Execution Vulnerability |
| CVE-2024-43523 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43524 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43525 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43526 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43533 | Distant Desktop Consumer Distant Code Execution Vulnerability |
| CVE-2024-43536 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43543 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43549 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43552 | Home windows Shell Distant Code Execution Vulnerability |
| CVE-2024-43564 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43574 | Microsoft Speech Utility Programming Interface (SAPI) Distant Code Execution Vulnerability |
| CVE-2024-43576 | Microsoft Workplace Distant Code Execution Vulnerability |
| CVE-2024-43581 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-43589 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43592 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43593 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43599 | Distant Desktop Consumer Distant Code Execution Vulnerability |
| CVE-2024-43601 | Visible Studio Code for Linux Distant Code Execution Vulnerability |
| CVE-2024-43607 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43608 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43611 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43615 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-43616 | Microsoft Workplace Distant Code Execution Vulnerability |
| CVE-2024-30092 | Home windows Hyper-V Distant Code Execution Vulnerability |
| CVE-2024-38029 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-38212 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38229 | .NET and Visible Studio Distant Code Execution Vulnerability |
| CVE-2024-38261 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| Reasonable Severity | |
| CVE-2024-43572 | Microsoft Administration Console Distant Code Execution Vulnerability |
| Low Severity | |
| CVE-2024-43497 | DeepSpeed Distant Code Execution Vulnerability |
Elevation of Privilege (28 CVEs)
| Essential severity | |
| CVE-2024-37979 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-38097 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2024-38124 | Home windows Netlogon Elevation of Privilege Vulnerability |
| CVE-2024-38129 | Home windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-38179 | Azure Stack Hyperconverged Infrastructure (HCI) Elevation of Privilege Vulnerability |
| CVE-2024-43501 | Home windows Widespread Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2024-43502 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43503 | Microsoft SharePoint Elevation of Privilege Vulnerability |
| CVE-2024-43509 | Home windows Graphics Part Elevation of Privilege Vulnerability |
| CVE-2024-43511 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43514 | Home windows Resilient File System (ReFS) Elevation of Privilege Vulnerability |
| CVE-2024-43516 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-43522 | Home windows Native Safety Authority (LSA) Elevation of Privilege Vulnerability |
| CVE-2024-43527 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43528 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-43529 | Home windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2024-43532 | Distant Registry Service Elevation of Privilege Vulnerability |
| CVE-2024-43535 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
| CVE-2024-43551 | Home windows Storage Elevation of Privilege Vulnerability |
| CVE-2024-43553 | NT OS Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43556 | Home windows Graphics Part Elevation of Privilege Vulnerability |
| CVE-2024-43560 | Microsoft Home windows Storage Port Driver Elevation of Privilege Vulnerability |
| CVE-2024-43563 | Home windows Ancillary Perform Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-43570 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43583 | Winlogon Elevation of Privilege Vulnerability |
| CVE-2024-43590 | Visible C++ Redistributable Installer Elevation of Privilege Vulnerability |
| CVE-2024-43591 | Azure Command Line Integration (CLI) Elevation of Privilege Vulnerability |
| CVE-2024-43604 | Outlook for Android Elevation of Privilege Vulnerability |
Denial of Service (26 CVEs)
| Essential severity | |
| CVE-2024-38149 | BranchCache Denial of Service Vulnerability |
| CVE-2024-43483 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43484 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43485 | .NET and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43506 | BranchCache Denial of Service Vulnerability |
| CVE-2024-43512 | Home windows Requirements-Primarily based Storage Administration Service Denial of Service Vulnerability |
| CVE-2024-43515 | Web Small Pc Methods Interface (iSCSI) Denial of Service Vulnerability |
| CVE-2024-43521 | Home windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-43537 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43538 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43540 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43541 | Microsoft Easy Certificates Enrollment Protocol Denial of Service Vulnerability |
| CVE-2024-43542 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43544 | Microsoft Easy Certificates Enrollment Protocol Denial of Service Vulnerability |
| CVE-2024-43545 | Home windows On-line Certificates Standing Protocol (OCSP) Server Denial of Service Vulnerability |
| CVE-2024-43555 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43557 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43558 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43559 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43561 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43562 | Home windows Community Handle Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-43565 | Home windows Community Handle Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-43567 | Home windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-43575 | Home windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-43603 | Visible Studio Collector Service Denial of Service Vulnerability |
| Reasonable severity | |
| CVE-2024-43520 | Home windows Kernel Denial of Service Vulnerability |
Safety Characteristic Bypass (7 CVEs)
| Essential severity | |
| CVE-2024-20659 | Home windows Hyper-V Safety Characteristic Bypass Vulnerability |
| CVE-2024-37976 | Home windows Resume Extensible Firmware Interface Safety Characteristic Bypass Vulnerability |
| CVE-2024-37982 | Home windows Resume Extensible Firmware Interface Safety Characteristic Bypass Vulnerability |
| CVE-2024-37983 | Home windows Resume Extensible Firmware Interface Safety Characteristic Bypass Vulnerability |
| CVE-2024-43513 | BitLocker Safety Characteristic Bypass Vulnerability |
| CVE-2024-43584 | Home windows Scripting Engine Safety Characteristic Bypass Vulnerability |
| CVE-2024-43585 | Code Integrity Guard Safety Characteristic Bypass Vulnerability |
Spoofing (7 CVEs)
| Essential severity | |
| CVE-2024-43481 | Energy BI Report Server Spoofing Vulnerability |
| CVE-2024-43550 | Home windows Safe Channel Spoofing Vulnerability |
| CVE-2024-43571 | Sudo for Home windows Spoofing Vulnerability |
| CVE-2024-43609 | Microsoft Workplace Spoofing Vulnerability |
| CVE-2024-43612 | Energy BI Report Server Spoofing Vulnerability |
| CVE-2024-43614 | Microsoft Defender for Endpoint for Linux Spoofing Vulnerability |
| Reasonable severity | |
| CVE-2024-43573 | Home windows MSHTML Platform Spoofing Vulnerability |
Data Disclosure (6 CVEs)
| Essential severity | |
| CVE-2024-43500 | Home windows Resilient File System (ReFS) Data Disclosure Vulnerability |
| CVE-2024-43508 | Home windows Graphics Part Data Disclosure Vulnerability |
| CVE-2024-43534 | Home windows Graphics Part Data Disclosure Vulnerability |
| CVE-2024-43546 | Home windows Cryptographic Data Disclosure Vulnerability |
| CVE-2024-43547 | Home windows Kerberos Data Disclosure Vulnerability |
| CVE-2024-43554 | Home windows Kernel-Mode Driver Data Disclosure Vulnerability |
Tampering (1 CVE)
| Essential severity | |
| CVE-2024-43456 | Home windows Distant Desktop Companies Tampering Vulnerability |
Appendix B: Exploitability
This can be a record of the October CVEs judged by Microsoft to be both below exploitation within the wild or extra prone to be exploited within the wild throughout the first 30 days post-release. The record is organized by CVE.
| Exploitation detected | |
| CVE-2024-43572 | Microsoft Administration Console Distant Code Execution Vulnerability |
| CVE-2024-43573 | Home windows MSHTML Platform Spoofing Vulnerability |
| Exploitation extra probably throughout the subsequent 30 days | |
| CVE-2024-43502 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43509 | Home windows Graphics Part Elevation of Privilege Vulnerability |
| CVE-2024-43556 | Home windows Graphics Part Elevation of Privilege Vulnerability |
| CVE-2024-43560 | Microsoft Home windows Storage Port Driver Elevation of Privilege Vulnerability |
| CVE-2024-43581 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-43583 | Winlogon Elevation of Privilege Vulnerability |
| CVE-2024-43609 | Microsoft Workplace Spoofing Vulnerability |
| CVE-2024-43615 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
Appendix C: Merchandise Affected
This can be a record of October’s patches sorted by product household, then sub-sorted by severity. Every record is additional listed by CVE. Patches which can be shared amongst a number of product households are listed a number of instances, as soon as for every product household.
Home windows (93 CVEs)
| Essential severity | |
| CVE-2024-43582 | Distant Desktop Protocol Server Distant Code Execution Vulnerability |
| Essential severity | |
| CVE-2024-20659 | Home windows Hyper-V Safety Characteristic Bypass Vulnerability |
| CVE-2024-30092 | Home windows Hyper-V Distant Code Execution Vulnerability |
| CVE-2024-37976 | Home windows Resume Extensible Firmware Interface Safety Characteristic Bypass Vulnerability |
| CVE-2024-37979 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-37982 | Home windows Resume Extensible Firmware Interface Safety Characteristic Bypass Vulnerability |
| CVE-2024-37983 | Home windows Resume Extensible Firmware Interface Safety Characteristic Bypass Vulnerability |
| CVE-2024-38029 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-38124 | Home windows Netlogon Elevation of Privilege Vulnerability |
| CVE-2024-38129 | Home windows Kerberos Elevation of Privilege Vulnerability |
| CVE-2024-38149 | BranchCache Denial of Service Vulnerability |
| CVE-2024-38212 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38261 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-38262 | Home windows Distant Desktop Licensing Service Distant Code Execution Vulnerability |
| CVE-2024-38265 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43453 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43456 | Home windows Distant Desktop Companies Tampering Vulnerability |
| CVE-2024-43500 | Home windows Resilient File System (ReFS) Data Disclosure Vulnerability |
| CVE-2024-43501 | Home windows Widespread Log File System Driver Elevation of Privilege Vulnerability |
| CVE-2024-43502 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43506 | BranchCache Denial of Service Vulnerability |
| CVE-2024-43508 | Home windows Graphics Part Data Disclosure Vulnerability |
| CVE-2024-43509 | Home windows Graphics Part Elevation of Privilege Vulnerability |
| CVE-2024-43511 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43512 | Home windows Requirements-Primarily based Storage Administration Service Denial of Service Vulnerability |
| CVE-2024-43513 | BitLocker Safety Characteristic Bypass Vulnerability |
| CVE-2024-43514 | Home windows Resilient File System (ReFS) Elevation of Privilege Vulnerability |
| CVE-2024-43515 | Web Small Pc Methods Interface (iSCSI) Denial of Service Vulnerability |
| CVE-2024-43516 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-43517 | Microsoft ActiveX Information Objects Distant Code Execution Vulnerability |
| CVE-2024-43518 | Home windows Telephony Server Distant Code Execution Vulnerability |
| CVE-2024-43519 | Microsoft WDAC OLE DB supplier for SQL Server Distant Code Execution Vulnerability |
| CVE-2024-43521 | Home windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-43522 | Home windows Native Safety Authority (LSA) Elevation of Privilege Vulnerability |
| CVE-2024-43523 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43524 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43525 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43526 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43527 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43528 | Home windows Safe Kernel Mode Elevation of Privilege Vulnerability |
| CVE-2024-43529 | Home windows Print Spooler Elevation of Privilege Vulnerability |
| CVE-2024-43532 | Distant Registry Service Elevation of Privilege Vulnerability |
| CVE-2024-43533 | Distant Desktop Consumer Distant Code Execution Vulnerability |
| CVE-2024-43534 | Home windows Graphics Part Data Disclosure Vulnerability |
| CVE-2024-43535 | Home windows Kernel-Mode Driver Elevation of Privilege Vulnerability |
| CVE-2024-43536 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43537 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43538 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43540 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43541 | Microsoft Easy Certificates Enrollment Protocol Denial of Service Vulnerability |
| CVE-2024-43542 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43543 | Home windows Cell Broadband Driver Distant Code Execution Vulnerability |
| CVE-2024-43544 | Microsoft Easy Certificates Enrollment Protocol Denial of Service Vulnerability |
| CVE-2024-43545 | Home windows On-line Certificates Standing Protocol (OCSP) Server Denial of Service Vulnerability |
| CVE-2024-43546 | Home windows Cryptographic Data Disclosure Vulnerability |
| CVE-2024-43547 | Home windows Kerberos Data Disclosure Vulnerability |
| CVE-2024-43549 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43550 | Home windows Safe Channel Spoofing Vulnerability |
| CVE-2024-43551 | Home windows Storage Elevation of Privilege Vulnerability |
| CVE-2024-43552 | Home windows Shell Distant Code Execution Vulnerability |
| CVE-2024-43553 | NT OS Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43554 | Home windows Kernel-Mode Driver Data Disclosure Vulnerability |
| CVE-2024-43555 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43556 | Home windows Graphics Part Elevation of Privilege Vulnerability |
| CVE-2024-43557 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43558 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43559 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43560 | Microsoft Home windows Storage Port Driver Elevation of Privilege Vulnerability |
| CVE-2024-43561 | Home windows Cell Broadband Driver Denial of Service Vulnerability |
| CVE-2024-43562 | Home windows Community Handle Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-43563 | Home windows Ancillary Perform Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2024-43564 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43565 | Home windows Community Handle Translation (NAT) Denial of Service Vulnerability |
| CVE-2024-43567 | Home windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-43570 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2024-43571 | Sudo for Home windows Spoofing Vulnerability |
| CVE-2024-43574 | Microsoft Speech Utility Programming Interface (SAPI) Distant Code Execution Vulnerability |
| CVE-2024-43575 | Home windows Hyper-V Denial of Service Vulnerability |
| CVE-2024-43581 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| CVE-2024-43583 | Winlogon Elevation of Privilege Vulnerability |
| CVE-2024-43584 | Home windows Scripting Engine Safety Characteristic Bypass Vulnerability |
| CVE-2024-43585 | Code Integrity Guard Safety Characteristic Bypass Vulnerability |
| CVE-2024-43589 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43592 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43593 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43599 | Distant Desktop Consumer Distant Code Execution Vulnerability |
| CVE-2024-43607 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43608 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43611 | Home windows Routing and Distant Entry Service (RRAS) Distant Code Execution Vulnerability |
| CVE-2024-43615 | Microsoft OpenSSH for Home windows Distant Code Execution Vulnerability |
| Reasonable severity | |
| CVE-2024-43520 | Home windows Kernel Denial of Service Vulnerability |
| CVE-2024-43572 | Microsoft Administration Console Distant Code Execution Vulnerability |
| CVE-2024-43573 | Home windows MSHTML Platform Spoofing Vulnerability |
Visible Studio (8 CVEs)
| Essential severity | |
| CVE-2024-43488 | Visible Studio Code extension for Arduino Distant Code Execution Vulnerability |
| Essential severity | |
| CVE-2024-38229 | .NET and Visible Studio Distant Code Execution Vulnerability |
| CVE-2024-43483 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43484 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43485 | .NET and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43590 | Visible C++ Redistributable Installer Elevation of Privilege Vulnerability |
| CVE-2024-43601 | Visible Studio Code for Linux Distant Code Execution Vulnerability |
| CVE-2024-43603 | Visible Studio Collector Service Denial of Service Vulnerability |
365 Apps (5 CVEs)
| Essential severity | |
| CVE-2024-43504 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-43505 | Microsoft Workplace Visio Distant Code Execution Vulnerability* |
| CVE-2024-43576 | Microsoft Workplace Distant Code Execution Vulnerability |
| CVE-2024-43609 | Microsoft Workplace Spoofing Vulnerability |
| CVE-2024-43616 | Microsoft Workplace Distant Code Execution Vulnerability |
* Regardless of the title, the data for this CVE doesn’t record any Visio-specific applicability
Workplace (5 CVEs)
| Essential severity | |
| CVE-2024-43504 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-43505 | Microsoft Workplace Visio Distant Code Execution Vulnerability* |
| CVE-2024-43576 | Microsoft Workplace Distant Code Execution Vulnerability |
| CVE-2024-43609 | Microsoft Workplace Spoofing Vulnerability |
| CVE-2024-43616 | Microsoft Workplace Distant Code Execution Vulnerability |
* Regardless of the title, the data for this CVE doesn’t record any Visio-specific applicability
.NET (4 CVEs)
| Essential severity | |
| CVE-2024-38229 | .NET and Visible Studio Distant Code Execution Vulnerability |
| CVE-2024-43483 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43484 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43485 | .NET and Visible Studio Denial of Service Vulnerability |
Azure (4 CVEs)
| Essential severity | |
| CVE-2024-38097 | Azure Monitor Agent Elevation of Privilege Vulnerability |
| CVE-2024-38179 | Azure Stack Hyperconverged Infrastructure (HCI) Elevation of Privilege Vulnerability |
| CVE-2024-43591 | Azure Command Line Integration (CLI) Elevation of Privilege Vulnerability |
| CVE-2024-43480 | Azure Service Cloth for Linux Distant Code Execution Vulnerability |
.NET Framework (2 CVEs)
| Essential severity | |
| CVE-2024-43483 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
| CVE-2024-43484 | .NET, .NET Framework, and Visible Studio Denial of Service Vulnerability |
Excel (2 CVEs)
| Essential severity | |
| CVE-2024-43504 | Microsoft Excel Distant Code Execution Vulnerability |
| CVE-2024-43609 | Microsoft Workplace Spoofing Vulnerability |
Energy BI (2 CVEs)
| Essential severity | |
| CVE-2024-43481 | Energy BI Report Server Spoofing Vulnerability |
| CVE-2024-43612 | Energy BI Report Server Spoofing Vulnerability |
Configuration Supervisor (1 CVE)
| Essential severity | |
| CVE-2024-43468 | Microsoft Configuration Supervisor Distant Code Execution Vulnerability |
DeepSpeed (1 CVE)
| Low severity | |
| CVE-2024-43497 | DeepSpeed Distant Code Execution Vulnerability |
Defender for Endpoint for Linux (1 CVE)
| Essential severity | |
| CVE-2024-43614 | Microsoft Defender for Endpoint for Linux Spoofing Vulnerability |
Outlook for Android (1 CVE)
| Essential severity | |
| CVE-2024-43604 | Outlook for Android Elevation of Privilege Vulnerability |
SharePoint (1 CVE)
| Essential severity | |
| CVE-2024-43503 | Microsoft SharePoint Elevation of Privilege Vulnerability |
Visible C++ (1 CVE)
| Essential severity | |
| CVE-2024-43590 | Visible C++ Redistributable Installer Elevation of Privilege Vulnerability |
Appendix D: Advisories and Different Merchandise
This can be a record of advisories and data on different related CVEs within the October launch.
| ADV990001 | Newest Servicing Stack Updates | |
| CVE-2024-6197 | CBL Mariner, Home windows | curl: CVE-2024-6197: releasing stack buffer in utf8asn1str |
| CVE-2024-7025 | Edge | Microsoft Edge Chromium: CVE-2024-7025 Integer overflow in Format |
| CVE-2024-9369 | Edge | Microsoft Edge Chromium: CVE-2024-9369 Inadequate information validation in Mojo |
| CVE-2024-9370 | Edge | Microsoft Edge Chromium: CVE-2024-9370 Inappropriate implementation in V8 |
| CVE-2024-43566 | Edge | Microsoft Edge (Chromium-based) Distant Code Execution Vulnerability |