Peter Shor revealed one of many earliest algorithms for quantum computer systems in 1994. Operating Shor’s algorithm on a hypothetical quantum laptop, one might quickly issue huge numbers—a seemingly innocuous superpower. However as a result of the safety of digital info depends on such math, the implications of Shor’s algorithm have been ground-shaking.
It’s lengthy been prophesied that trendy cryptography, employed universally throughout the gadgets we use each day, will die by the hands of the primary sensible quantum laptop.
Naturally, researchers have been trying to find safe alternate options.
In 2016, the US Nationwide Institute of Requirements and Expertise (NIST) introduced a contest to create the primary post-quantum cryptographic algorithms. These packages would run on immediately’s computer systems however defeat assaults by future quantum computer systems.
Starting with a pool of 82 submissions from around the globe, NIST narrowed the record to 4 in 2022. The finalists glided by the names CRYSTALS-Kyber, CRYSTALS-Dilithium, Sphincs+, and FALCON. This week, NIST introduced three of those have develop into the primary standardized post-quantum algorithms. They’ll launch a regular draft of the final, FALCON, by the top of the yr.
The algorithms, based on NIST, symbolize one of the best of one of the best. Kyber, Dilithium, and FALCON make use of an method referred to as lattice-based cryptography, whereas Sphincs+ makes use of an alternate hash-based technique. They’ve survived a number of years of stress testing by safety specialists and are prepared for speedy use.
The discharge consists of code for the algorithms alongside directions on how one can implement them and their meant makes use of. Like earlier encryption requirements developed by the company within the Nineteen Seventies, it’s hoped huge adoption will guarantee interoperability between digital merchandise and consistency, decreasing the danger of error. The primary of the group, renamed ML-KEM, is for normal encryption, whereas the latter three (now ML-DSA, SLH-DSA, and FN-DSA) are for digital signatures—that’s, proving that sources are who they are saying they’re.
Arriving at requirements was a giant effort, however broad adoption might be larger.
Whereas the concept that future quantum computer systems might defeat customary encryption is pretty uncontroversial, when it would occur is murkier. Right now’s machines, nonetheless small and finicky, are nowhere close to as much as the duty. The primary machines capable of full helpful duties quicker than classical computer systems aren’t anticipated till later this decade on the very earliest. However it’s not clear how highly effective these computer systems should be to interrupt encryption.
Nonetheless, there are strong causes to get began now, based on proponents. For one, it’ll take so long as 10 to fifteen years to roll out post-quantum cryptography. So, the sooner we kick issues off the higher. Additionally, hackers could steal and retailer encrypted knowledge immediately with the expectation it may be cracked later—a technique often known as “harvest now, decrypt later.”
“Right now, public key cryptography is used in every single place in each gadget,” Lily Chen, head of cryptography at NIST, instructed IEEE Spectrum. “Now our job is to interchange the protocol in each gadget, which isn’t a simple job.”
There are already some early movers, nonetheless. The Sign Protocol underpinning Sign, WhatsApp, and Google Messages—merchandise utilized by greater than a billion individuals—carried out post-quantum cryptography primarily based on NIST’s Kyber algorithm alongside extra conventional encryption in late 2023. Apple did the identical for iMessages earlier this yr.
It’s notable each opted to run the 2 in parallel, versus going all-in on post-quantum safety. NIST’s algorithms have been scrutinized, however they haven’t been out within the wild for almost so long as conventional approaches. There’s no assure they gained’t be defeated sooner or later.
An algorithm within the operating two years in the past, SIKE, met a fast and surprising finish when researchers took it down with some intelligent math and a desktop laptop. And this April, Tsinghua College’s, Yilei Chen, revealed a pre-print on the arXiv wherein he claimed to point out lattice-based cryptography really was weak to quantum computer systems—although his work was later proven to be flawed and lattice cryptography nonetheless safe.
To be protected, NIST is creating backup algorithms. The company is at present vetting two teams representing various approaches for normal encryption and digital signatures. In parallel, scientists are engaged on different types of safe communication utilizing quantum techniques themselves, although these are possible years from completion and could complement moderately than exchange post-cryptographic algorithms like these NIST is standardizing.
“There is no such thing as a want to attend for future requirements,” mentioned Dustin Moody, a NIST mathematician heading the mission, in a launch. “Go forward and begin utilizing these three. We must be ready in case of an assault that defeats the algorithms in these three requirements, and we are going to proceed engaged on backup plans to maintain our knowledge protected. However for many purposes, these new requirements are the principle occasion.”
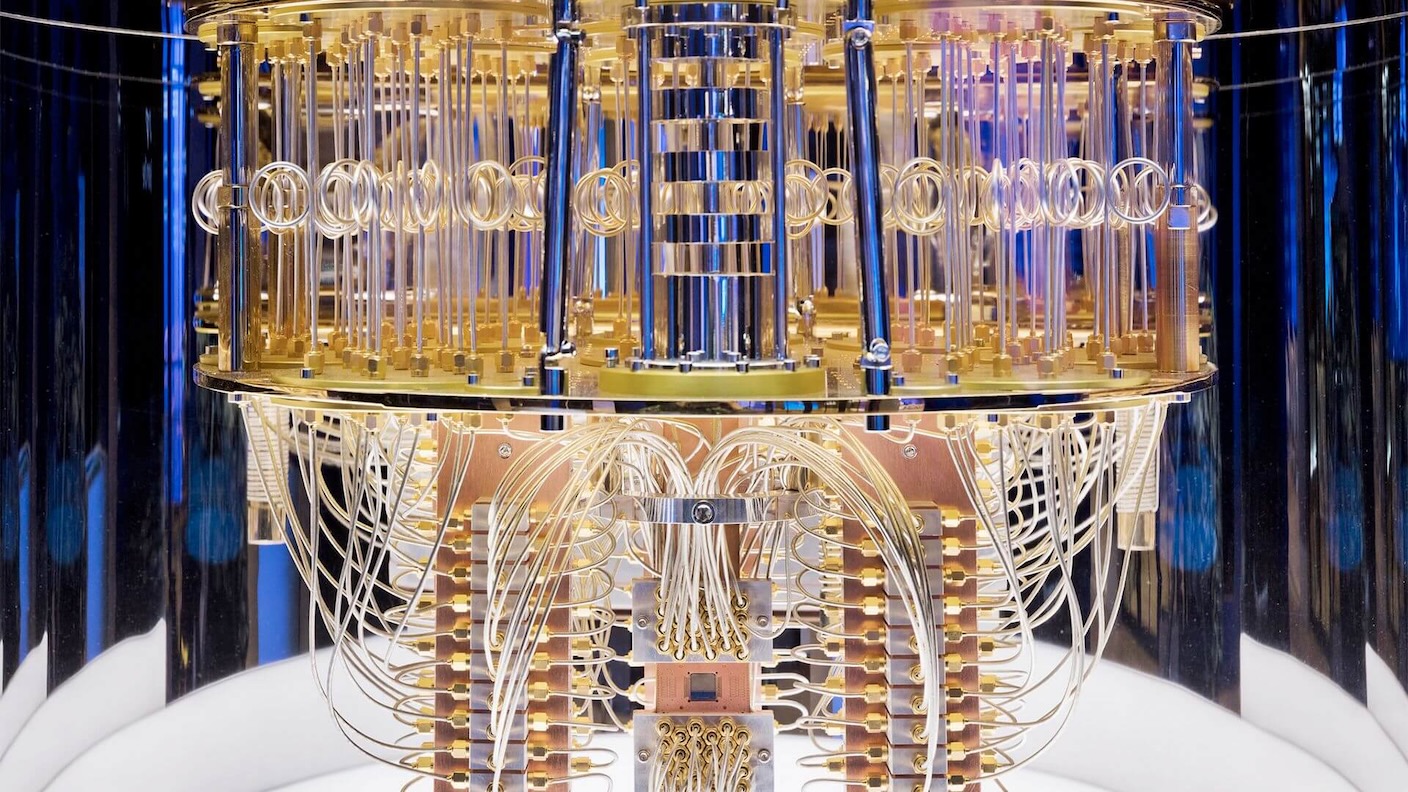
Picture Credit score: IBM